What exactly does quantum count threaten? A Crypto user guide to the back quantum age
Quantum threats are real, but they are far from being "imminent" and it is even more critical to find out what encoded components will affect and how the industry is preparing to move。
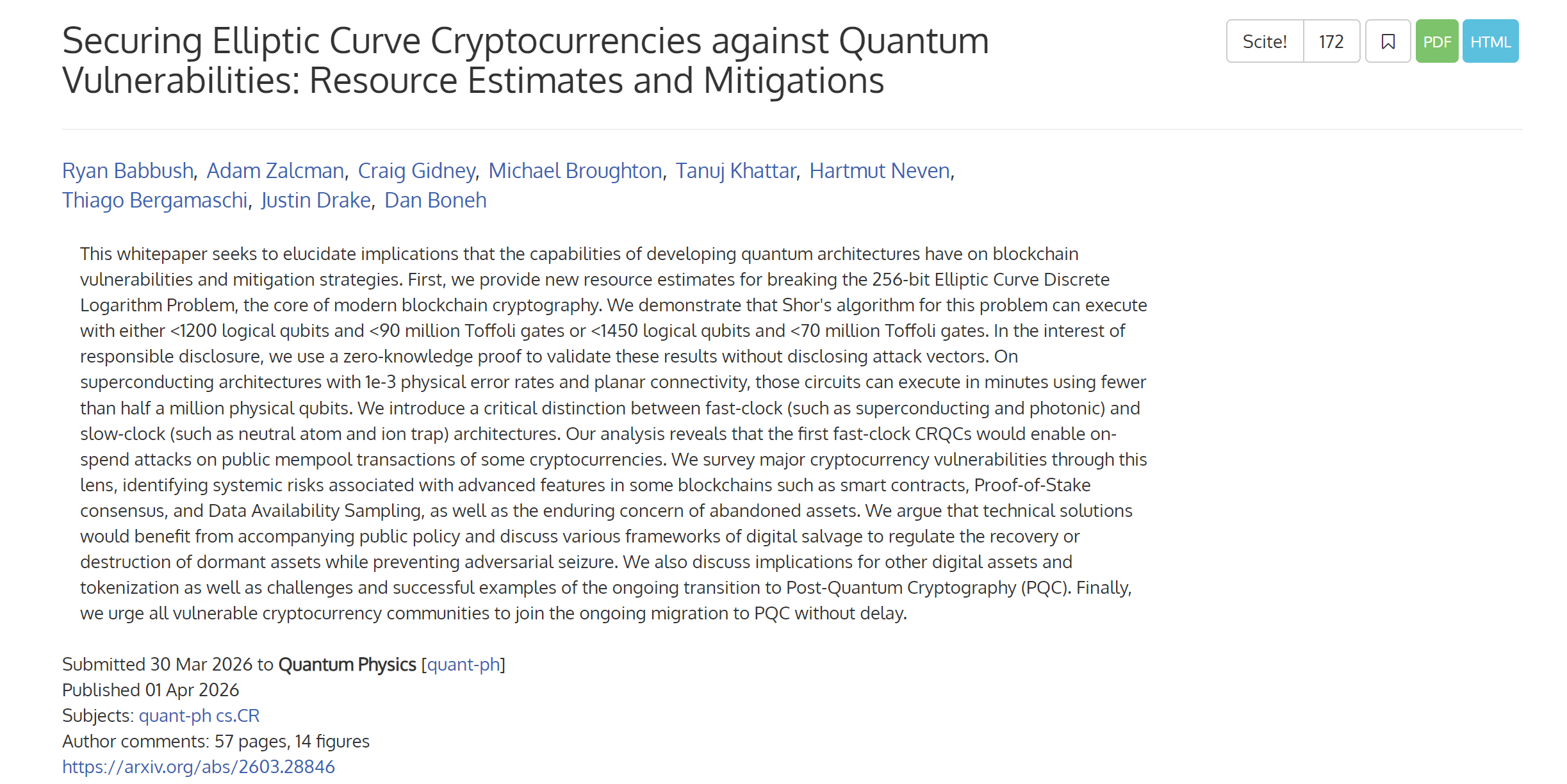
Just last week, the Google Quantum AI team published a heavy-pound paper stating that, under superconductive structures, specific error correction and hardware assumptions, the future quantum computer could use fewer than 500,000 physical quantum bits to break, within minutes, the 256-digit elliptical curve password (ECDLP-256), widely used in encrypted currencies and block chains, and that the number of quantum bits required was approximately 20 times lower than previously estimated。
THIS DIRECTLY POINTS TO THE CORE OF THE SIGNATURE PROGRAM FOR ALMOST ALL MAINSTREAM PUBLIC CHAINS, SUCH AS BITCOIN, ETHERLEAF, AND AS SOON AS WORD COMES OUT, THE CLAIM THAT QUANTUM COMPUTERS ARE GOING TO DECIPHER BITCOIN'S PRIVATE KEY IS STARTING TO GO ONLINE。
In fact, we need to calm down and make it clear — the threat is real — but it is still a long way from “your wallet is not safe tomorrow”。
More importantly, the whole industry was already in action。
1. What is the threat of quantum calculations
To understand this, we start with the basics of your Cripto asset, how was it protected
It is well known that each account has a pair of keys: a private key and a public key, either in bitcoin or in the Ether factory. Of these, the private key is a series of randomly generated large numbers, extremely confidential, equivalent to the password of your safe; the public key is derived from the private key by an elliptical curve multiplication, and your wallet address is a string that the public key is then compressed through the Hashi function。
The security underpinning of the system is precisely that the process is one-way。
AFTER ALL, IT IS EASY TO CALCULATE A PUBLIC KEY FROM A PRIVATE KEY, BUT IT TAKES MUCH LONGER THAN THE AGE OF THE UNIVERSE TO PUSH THE PRIVATE KEY FROM A PUBLIC KEY, WHICH IS ALSO THE ESSENCE OF THE "ELIPTICAL CURVE FRAGMENTING LOGIC" (EDCLP) -- WHICH IS SIMPLE TO CALCULATE AND IMPOSSIBLE TO REVERSE。
But quantum computers break this assumption, and it solves the problem of integer and discrete logarithms over time, in other words, a quantum computer that is strong enough to theoretically push your private key back from your public key。
Then the question is, when will the public key be exposed
Every time you start a transaction with a block chain, you need to sign the transaction data with a private key and broadcast your public key for validation, which means that as long as you make a deal, your public key is already on the chain。
The point of this paper, Google, is to move the "break private key from a public key" from a theoretically feasible, but ridiculous, point to a programmable goal on the quantum hardware road map, which, according to the paper, deciphers 256 bits of ECDLP, requires approximately 500,000 physical quantum bits of faulty quantum computers, significantly lower than previously estimated。
In the final analysis, quantum calculations are not breaking the block chain, but are aimed first at a signature system in the block chain that is still based on the fissure of the elliptical curve。
So, the threat is real, but technically, the term "imminent" is not accurate, and industry mainstream estimates give a window period that is still around 2030Native accounts abstract + Quantum Threat: EIP-8141 why is it not the top of Hegotá)。
II. What are the public chains prepared for
Of course, objectively, there is a key difference, and many stories are not clear, so many bitcoin addresses do not reveal public keys directly in the chain at the outset。
IN COMMON FORMS SUCH AS P2PKH, P2WPKH, THE ADDRESS ITSELF IS USUALLY A HUSHI OF A PUBLIC KEY, WHICH OFTEN WAITS UNTIL THE "FIRST COST" IS REVEALED, WHICH MEANS THAT IF YOUR ADDRESS NEVER SENDS A TRANSACTION, ONLY YOUR WALLET ADDRESS IS ON THE CHAIN, AND THERE IS NO PUBLIC KEY。
Thus, the most direct face of the quantum calculation is the public key that favours those addresses that have been traded. Of course, this detail leads directly to the first thing that can be done at the user level now, and we will talk about it later。
The industry is not unaware of this problem and, in fact, preparations for the migration of late quantum codes are advancing simultaneously on multiple fronts。
The answer is to untie the account level and the signature programFOR EXAMPLE, THE ADVANCE OF EIP-7702 AND THE ABSTRACT ACCOUNT (AA) ALLOWS THE TAIFENG ACCOUNT TO DEFINE WHAT IS CALLED A LEGAL SIGNATURE BY INTELLIGENT CONTRACT LOGIC, WHICH MEANS THAT WHEN THE QUANTUM SIGNATURE PROGRAM IS INTRODUCED AT A FUTURE DATE, IT IS NOT NECESSARY TO REWRITE THE BOTTOM OF THE PROTOCOL, BUT SIMPLY TO REPLACE THE SIGNATURE VALIDATION MODULE OF THE ACCOUNT。
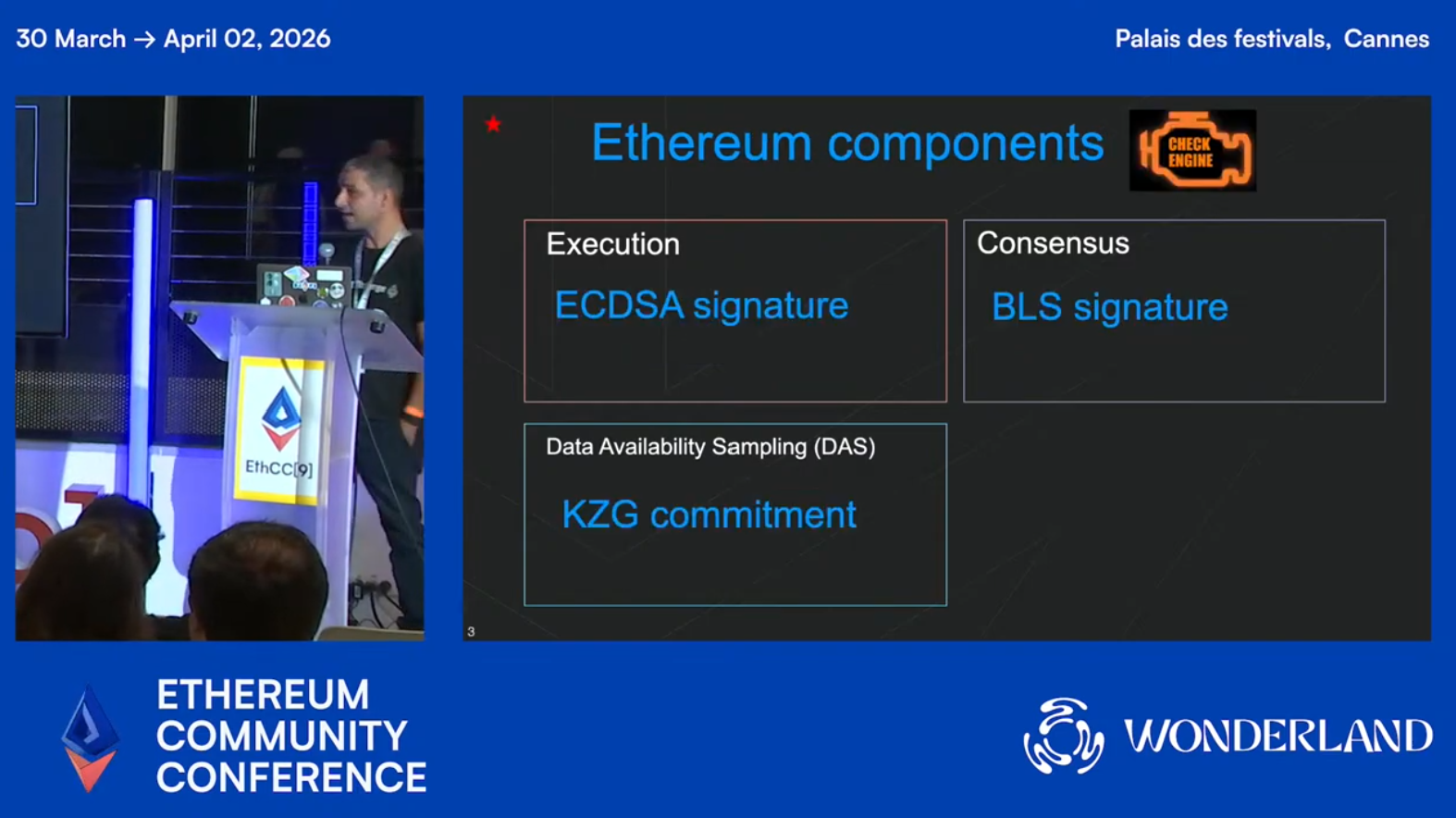
To go further, Antonio Sanso, a password researcher at the EthCC9 Foundation, updated the latest developments in EtherCC9 on the security of quantum resistance at the EthCC9 conference, noting that quantum computers could pose a real threat to the ECDSA signature algorithm in the mid-2030s, that approximately 20 per cent of the resistance is now being prepared at the Taifah and that full quantum resistance is planned to be achieved through the Lean Etherum upgrade between 2028 and 2032。
However, the main technical challenge is the size of the signature, which, like the lightweight late quantum signature algorithm Falcon, is still 10 times the size of the ECDSA, and the Gas cost of verifying Lattice-based directly in Solidity is extremely high, so the team established two core technical pathways:
- One is to allow users to upgrade the wallet signature algorithm to an antiquator programme through the abstraction of the account, without the need to modify the bottom protocol
- Second, the introduction of LeanVM to handle complex Hashi operations and to safeguard the security of assets in the course of relocation by combining zero-knowledge proof of ownership of address assistive notes
Antonio has indicated that a two-week post-ACD quantum conference will be hosted from February 2026 and that consensus clients such as Lighthouse and Grandine are now on-line on-line experimental post-quantum testing networks。
In addition to thisIt is clear that the style of the Bitcoin community is more conservativeBIP360, which recently entered the BIPs repository, proposed a new type of output P2MR (Pay-to-Merkle-Root), one of its design objectives being to remove the weak Quantum in Taproot and to set a more friendly structure for possible later quantum signature migration in the future。
Of course, the entry of a proposal into the BIPs warehouse does not mean that a community consensus has emerged, let alone that it is about to be adopted, so that more specific proposals have already been discussed within the Bitcoin community around quantum exposures and changes in potential output types, which is also consistent with the usual Bitcoin style, which starts with a clear definition of the problem and then a very slow consensus。
IT IS WORTH NOTING THAT, AS EARLY AS 2024, THE NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY (NIST) OF THE UNITED STATES OFFICIALLY ISSUED THREE POST-QUANTITATIVE CODE STANDARDS, WHICH MEANT THAT THE BLOCK CHAIN ECOLOGY HAD A CLEAR MIGRATION TARGET AND NO LONGER NEEDED TO WAIT FOR A BETTER DISCUSSION OF THE ALGORITHM, AND THAT THE PROJECT HAD BEEN SUBSTANTIALLY STARTED。
What should ordinary users do
While the threat of quantum computers is a matter of years, what follows does not mean that it is not a matter of now. There are some good habits that are being developed today at almost zero。
First of all, it is the most immediate and effective measure of self-protection to avoid re-use of the address。
AND THAT'S WHY -- IF YOU'RE A UTXO CHAIN USER LIKE BITCOIN, EVERY TIME YOU START A TRANSACTION, YOUR PUBLIC KEY IS EXPOSED TO THE CHAIN, AND IF YOU USE THE SAME ADDRESS EVERY TIME, THE PUBLIC KEY IS LONG-TERM OPEN, AND ONCE THE QUANTUM IS MATURE, THE AGGRESSOR CAN EASILY PUSH THE PRIVATE KEY FROM YOUR PUBLIC KEY。
Now mainstream wallets like imToken have provided HD wallets by default. It's a good habit to receive a new address every time a transfer is made, not to repeat an address as a permanent identifier, andFor those addresses where no transaction has ever been made, the public key has never been revealed, and the current quantum threat is hardly applicable。
The second concerns the rear quantum upgrade route of the wallet。
If you mainly use a model account chain like the Taifeng, then the focus is not on mechanical change of address, but on the wallet and the public chain you use, and whether there is a clear migration path in the future。
Because the larger problem of the quantum age for the account model chain is often not a single exposure, but rather a long-term binding of active accounts, public key history, chain identity and application privileges, whose accounts are more scalable as soon as they actually enter the migration window, and whose wallets are smoother to replace signature logic。
And finally, from a human point of view, it is foreseeable that, as the heat of the topic rises, there will be more and more wallets or agreements on the market claiming "quantum safety", and we should be alert to those wallets, protocols and infrastructure products under the banner "quantum safety"。
In the face of such claims, the most important question to be asked is not propaganda, but three more hard questions:
- DOES IT RELY ON ALGORITHMS THAT NIST HAS FINALIZED?
- Has its security been independently audited and fully validated?
- Does it claim to be chain migration, account upgrades, or is it just application layer packaging
After all, the real late quantum is safe, and ultimately not just an App label, but a whole path from signature, authentication to chain compatibility。
In general, the threat to the chain of blocks from quantum calculations is real, and the importance of Google, the latest white paper, is indeed that it brings the threat one step closer from distant theory to programmable risk。
But it is still not a signal that the wallet will be broken tomorrow, and it is more precisely understood that later quantum migration is no longer an academic-only topic, but rather a reality that will move into upgrading protocols, wallet design, and user asset management over the coming years。
At the end
And what's really important for the industry is not who calls the quantum first, but who can design the migration path first。
For users, it is not the time to be in a panic, but to build on the most basic perceptions of risk:Which assets are first exposed, which operations will magnify exposure, and which wallets and public chains are more likely to provide smooth upgrades in the future。
What we need is early action, not excessive anxiety。
We're all here。