From the Kelp DAO event to Verifiable UI: Why is the "verifiable interface" a new decentralised safety floor
A security accident once again exposed DeFi's trust in single-point validation, layer-set default, which continues to rely on massively until today。

On the chain, DeFi's world, there's another double-crossing security accident of billions of dollars。
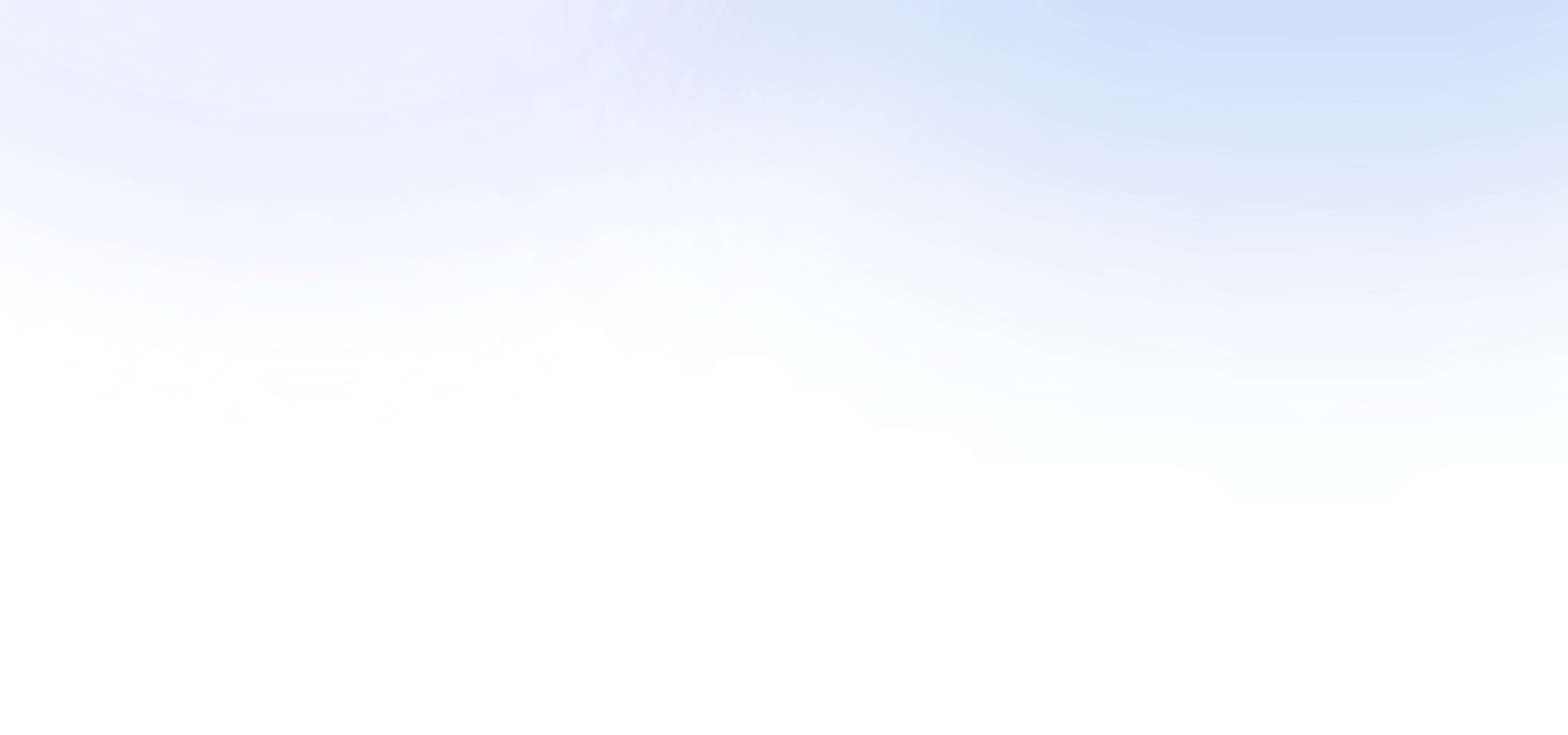
On 18 April, using 1-of-1 DVD of Kelp DAO's Layer Zero route, and without a configuration of alternative verifiers, the attackers falsely released 116,500 rsETHs of contracts, leaving Aave facing potentially bad debts of between $123.7 million and $230.1 million in different loss-sharing scenarios。
To be objective, this is not only the largest DeFi security incident since 2026, but more crucial is to pierce a structural assumption that the entire industry has accepted before:In the interest of efficiency, liquidity and profitability, increasing security is being quietly invested in a few default credible intermediates。
First, the failure of the decentralised mechanism behind the Kelp DAO
If the Kelp DAO event is understood as an ordinary chain security wave, it is easy to underestimate its implications for the entire DeFi structural risk。
Kelp DAO, as a Liquid Restanking (mobile re-commitment) protocol in the Pacifican ecology, theoretically users can obtain rsETH as a certificate, not only in the main web, but also in the standard OFT envelope of LayerZero, which is deployed on 20 chains such as Base, Arbitrum, Linea, Blast, Mantle, Scroll, etc。
In other wordsThe inter-chain contract on the other side of the ETPC keeps all the ETH reserves, while the rest of the chain is essentially a “bill of lading for the main network reserve”THIS ALSO MEANS THAT THE SYSTEM IS BASED ON THE PREMISE THAT THE ANCHORAGE OF "THE NUMBER OF ANCHORS IN THE MAIN NETWORK IS ALWAYS GREATER THAN OR EQUAL TO THE NUMBER FOUND ON THE L2 CHAIN" CANNOT BE DESTROYED。
And what the attacker did was the bottom of what seemed to be a simple but crucial constraint. He simply forged a "legitimate" "lawful" "LayerZero" cross-link, convinced the main bridge contract that it was a payment order from other chains of compliance and released 116,500 rsETHs。
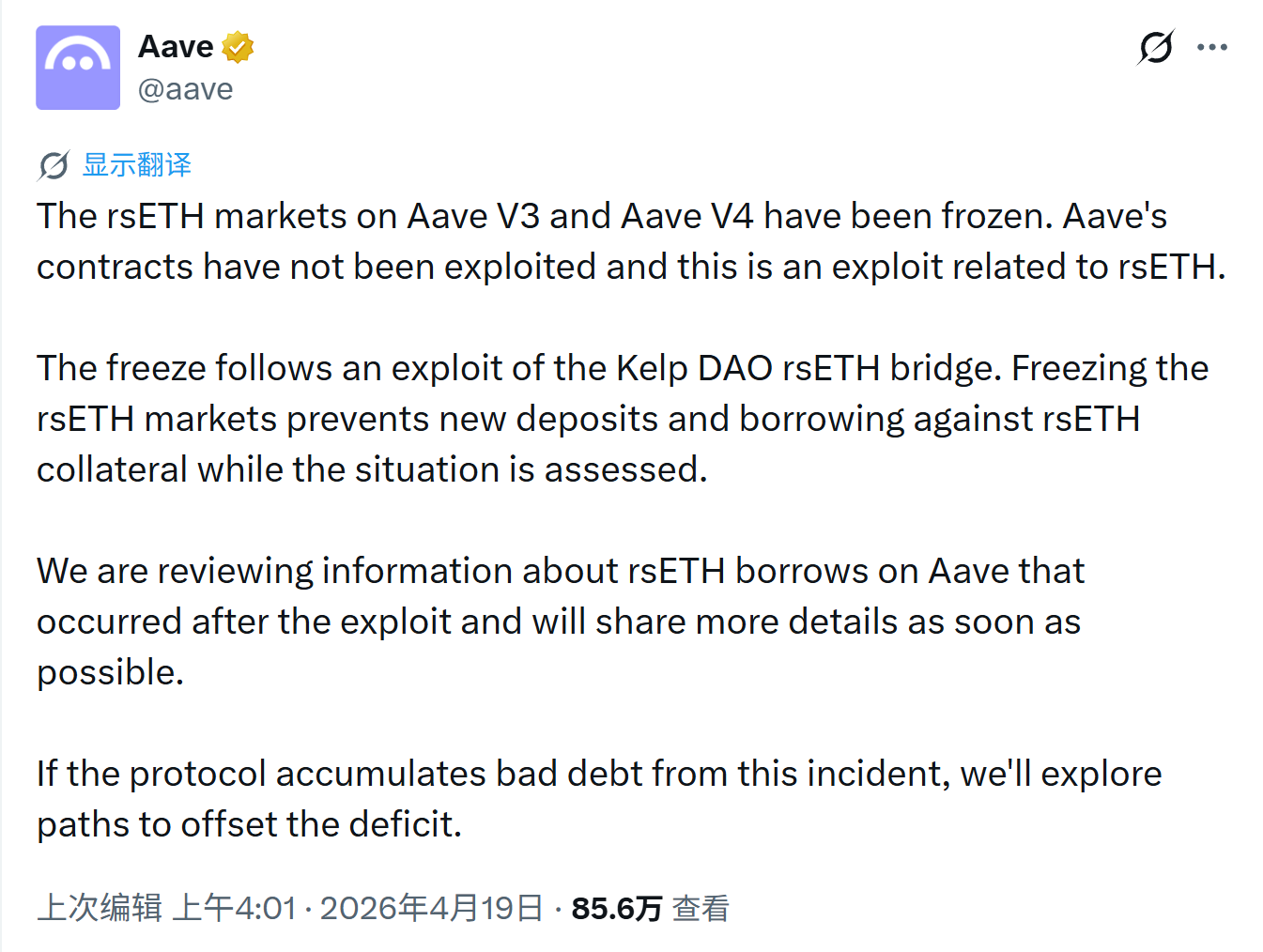
The key to the problem is hidden in LayerZero's authentication configurationKelp DAO uses 1/1 DVD configuration, allowing a authentication node to sign enough to release a cross-link messageAnd Officer LayerZero is actually recommending 2/2 and even multiple certifier redundancy, and this 1/1 risk has been publicly warned by security researchers as early as January 2025, but has not been modified in 15 months
This is why it is difficult to simply classify the incident as "the bridge has been blacked" or "a certain agreement has not been sufficiently controlled", which exposes a two-layered, single-point risk:
- The first level is certification single points: the DVN is theoretically designed as a combination of X-of-Y-of-N security models that support multiple independent validations to meet different security needs, but the legitimacy of the whole message in KelpDAO is reduced to a "no problem with a validation node" assumption
- The second level is the single point of the reserve: once the main network reserve pool is punctured, the rsETH on the other chain immediately ceases to be a cross-chain asset and exposes the essence of IOU, which is built on a single main network anchor
WhenIf a single point of authentication and a single point of stock are stacked together, the risk will no longer remain within a single agreement, but will spill along DeFi ' s portfolio。
This is why Aave immediately frozen the rsETH/wrsETH market after the accident, adjusted the WETH interest rate model, and further frozen several WETH markets to prevent pressure from spreading to more assets. Even though Aave himself was not hacked, the collateral was compromised, liquidation blocked, the borrower ' s health put him at risk of material bad debts。
And if the perspective is raised, the logic of “outsourcing safety to a single point” is not only present at the bridge and at the certifier, but also at a point where users face each day, but are rarely positively discussed — the interface。
ii. From "assets self-custody" to "interactive validation": the most easily ignored single point of trust
Web3 community has an old saying: Don't trust, Verify。
The ETA official's interpretation of the sentence in introducing the node is quite straightforward: running your own node means you don't need to believe what someone tells you, because you can validate the data yourself, not outsource it to a central data provider。
This principle is put in the wallet and DeFi interface, which is equally valid。
Non-host wallets like imToken, which are essentially users' access to accounts, are your "seeing assets, sending transactions, login applications" window. The wallet itself does not trust your money, nor does the private key hold it on the platform. Over the past few years, the industry has also come to accept the importance of the "asset trust" issue, and more and more people are beginning to understand the real decentrization, not just by placing the currency in the chain, but by handing over control of the asset to the user himself。
But the problem is that, while we are placing increasing emphasis on “self-custody” at the asset level, there is still a great deal of acquiescence at the cross-cutting level for a more subtle outsourcing, that is, understanding the meaning of the transaction, judging the outcome of the call, and giving trust in the authenticity of the interface to this front-end of the moment。
This is precisely one of the most vulnerable risks of DeFi today:Did the user sign the deal he thought he was signing
It can be said that in the day-to-day chain interaction, users are faced with almost no chain per se, but with a layer of packaged interfaces, such as the DApp front end of the web page, a wallet window, a routing statement given by the polymer, and that the future will also include the automatic call and confirmation of the result of Agent, which will tell you that "you are depositing 100 ETH into a strategy", "you will get some annual gain", "you are just making an ordinary mandate."。
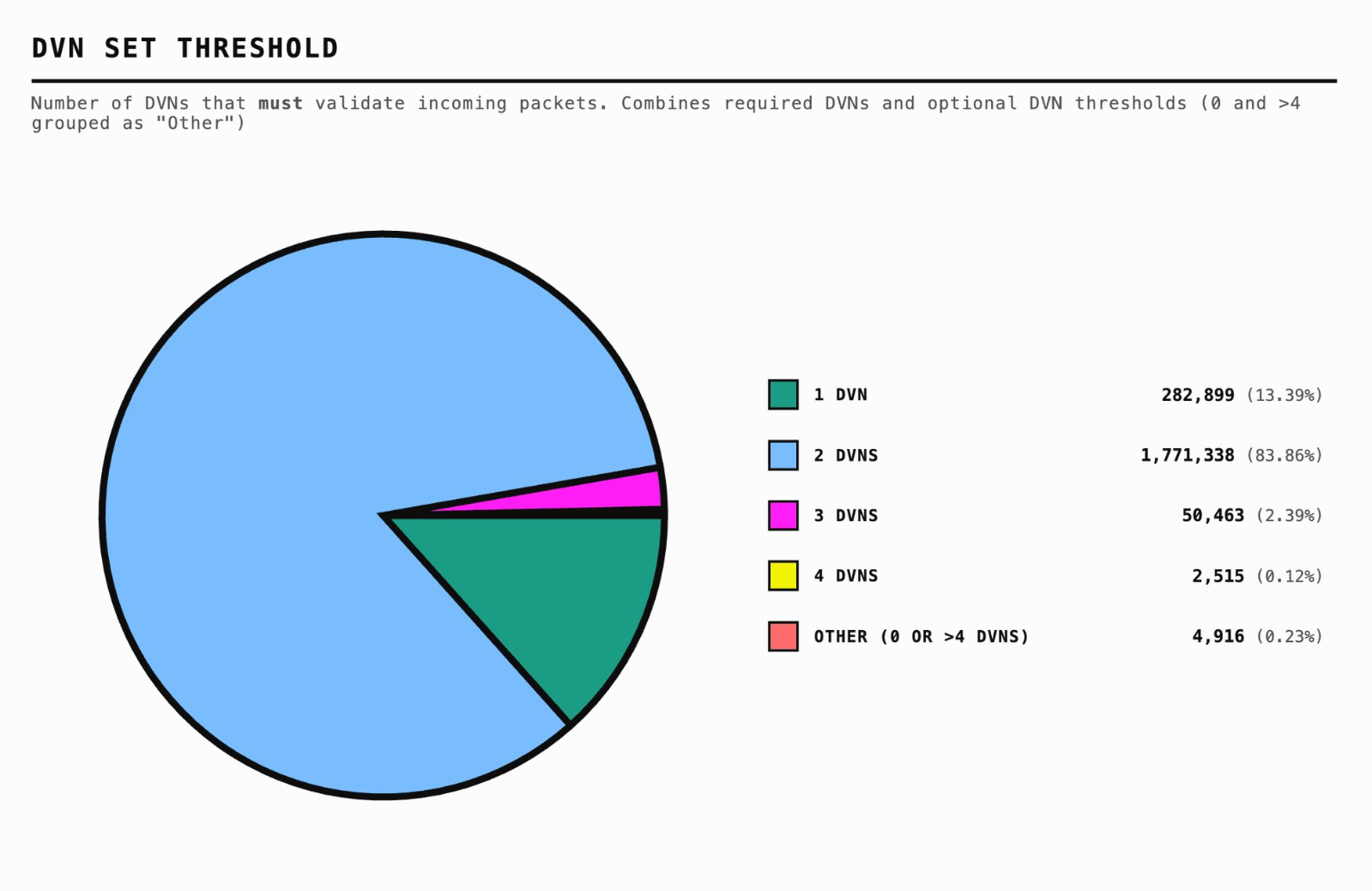
but what is the calldata that is actually signed, broadcast and chained, and whether the front-end description is strictly consistent with the bottom-level execution, and most users do not have the capacity to independently check it。
And that's why, historically, there are recurring front-end hijackings, address substitutions, malicious authorization disguises that appear to be different types of security incidentsThe bottom line is actually pointing to the same problem, that is, the transaction signed by the user, not always the one he thinks he signed。
From this point of view, the Kelp DAO event did not only expose the single-point validation issue in the bridge path, but it was a logical reminder of another long-overdue underestimation of the industry as a whole, i.e., in many chain interactions, the interface itself is a single point of default that is trusted but rarely validatedThe moment you clicked "Acknowledge," you were actually putting the call right and betting on "the interface is not lying."。
It also introduces the concept of "Verifiable UI"。
"Verifiable UI" is a "verifiable interface". It's not about making the front end better, it's not about writing the signature window more popular, it's about tryingThe content presented in the interface is linked to a call that can be verified by the user, validated by the wallet, or traced afterwards。
In other words, what it wants to do is not "does the information show or not" but "does it really correspond to what's going on in the chain," which means:
- the wallet, before signing, should not simply be shown to the user a sequence of hexadecimal data, nor should it simply reproduce a one-sided narrative created by the front end, but should, as far as possible, return the namedata to human readable and semantic operational intent
- Each step described by the interface should also be capable of mapping verifiable evidence on the chain, rather than resting on a set of interpretative logics that users believe are valid
- Only then will the gap between what you think you're doing and what's really happening on the chain cease to be a hard-to-reach cognitive divide
When this is established, the interface is no longer a glass window that allows users to believe but cannot independently verify it, more like an implementation instruction that the user can personally confirm and can go back。
If only to look at DeFi today, the validation of the interface remains a subject of serious underestimation; but if the timescale is slightly longer, it will soon move from “security optimization worthy of discussion” to “basic capability that cannot be further delayed.” Because of its interactive path, there is a quiet but far-reaching migration。
Three, Verifiable UI
If the Kelp DAO event is exposed to a single point of confidence problem that has existed for many years in the old DeFi architecture, then the "Verifiable UI" is a new phase that has already begun。
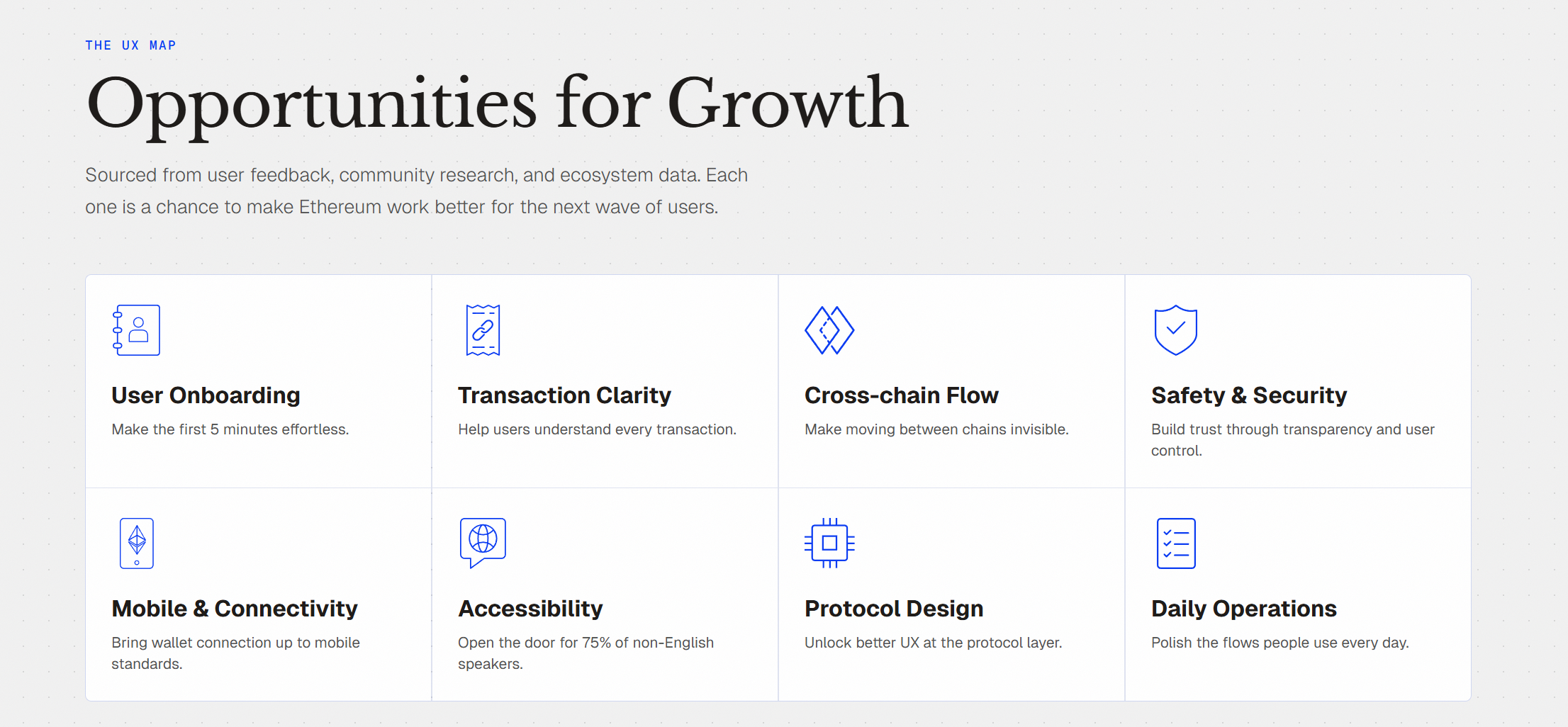
ETHUX, an ETA UX graphic, has clearly combed the core of today's interactions on the chain: Transaction Clarity, Cross-chain Flow, Safety & Security has always been the core category of pain point, blind signing, signing fatigue, Bridging pain, asset formation, and almost every old user is familiar with these problems。
WHAT'S BEHIND THIS IS NOT THAT "USER EDUCATION ISN'T ENOUGH," BUT THAT'S A MORE FUNDAMENTAL FACT. UX AND SECURITY ARE NEVER THE SAME IN THE CHAIN WORLD。
In other words, in many cases, it is the greatest security risk in itself。
And as the interactive paradigm moves from "user clicks one step at the front end of the DApp" to "user expression of intent, the system automatically completes implementation", the problem will only be magnified and will not be weakened。
After all, in the traditional front-end era of DApp, users can at least see buttons, pages, authorized windows, even if they are not fully understood, and can at least blur the perception of "I'm doing a few steps," "this is an authorization or a transfer", "I'm crossing the chain or a deposit."。
But once we enter the Age of Age, this visible process sense will be significantly reduced. Users are no longer opening up points by point, Router, Bridge, Vault, Lending Market to confirm every call, but are more likely to say to AI's wallet: "Turn my ETH into a more stable revenue strategy", "Base to Base, control the maximum slide point" and "only allow this Agent to spend 100 USDT within 24 hours" and wait for a "completed" result。
This, of course, means a significant increase in efficiency, but it also means that intermediate paths, parameters, authorizations, implementation sequences are becoming more and more susceptible to folding out of user view. And it's against this background that imtoken suggested two parallel directionsOne is to continue exploring an interactive path based on intent, to allow users to express "what I want" and the system to find a path and complete implementation; the other is to advance the "Unified & Amp; Verifiable UI" to bring the "interface itself could be a face of attack" explicitly to the long term proposition at the product level。
This is actually the most crucial shift in duties for the next generation's wallet。
In the past, the wallet was more like a signature tool to send user confirmation actions to the chain; instead, at the stage of Agent ' s gradual involvement in the interactive process, the wallet could not be a single channel, but must be the last definitive check point before execution. AI can be responsible for understanding demand, generating programs, planning paths, but the wallet must be responsible for producing these probabilities and translating them into definitive enforcement elements that the user can validate, the system can validate and the rules can bind。
In this sense, what really corresponds to "Verifiable UI" is not a higher-level interface design concept, but a new interactive security model, or even a new oneIt's more like a bottom puzzle that almost always has to be completed after the next phase of the wallet。
In the past, the industry has emphasized "not your keys, not your coins," but in an era when the intention was to drive and implement Agent, it was necessary to add the following sentence: Your interface should also be one that you can validate。
At the end
In the wake of the Kelp DAO incident, there was a great deal of discussion in the industry about the DVD configuration, LRT wind control, bridge paths and single point risk screening。
These discussions have their merits。
But if an accident at the cost of hundreds of millions of dollars is finally summed up as "who signed less" it is not really understoodIt is even fitting to say that the efficiency, liquidity and benefits of many of today ' s chain products are still based on single-point assumptions that users cannot see or verify。
That is why centralization is never the opposite of efficiency, but the bottom line of safety。
The era of building security on a single-point scenario needs to end。